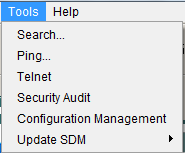
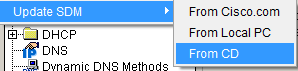
let's start with Search SDM features :
this interface explain itself
enter any feature in cisco sdm dhcp ,dns, vpn ,....
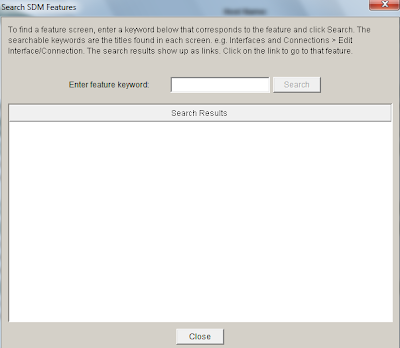
in this example I entered interface and click search this is the result
show you any related to interface features in cisco sdm and how you can reach it in a simple and easy way just click it
 this is the result after clicking the Search SDM feature
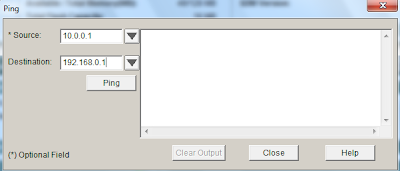
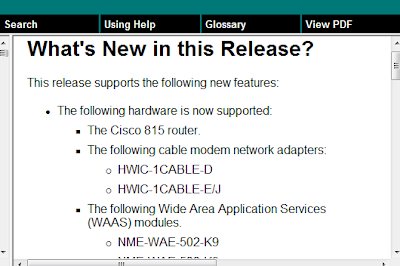
this is the result after clicking the Search SDM feature now lets move to the biggest and the most important part SDM help:
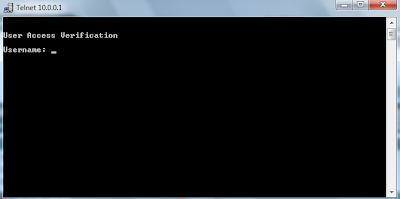
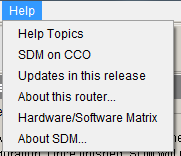
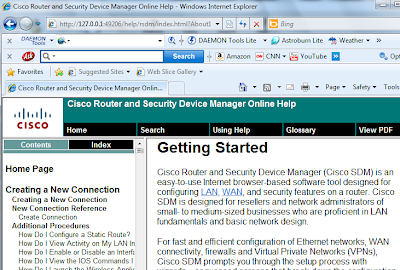
now lets move to the biggest and the most important part SDM help:this is the Cisco SDM Help cisco document every tiny bit in their Help to provide you a complete help system
 in any interface you don't understand it you need any more help or explain to you what this interface do just help help
in any interface you don't understand it you need any more help or explain to you what this interface do just help helpin this example i click help at security audit
 at the left side of cisco help system window you can arrange index (from A to Z ) or related contents
at the left side of cisco help system window you can arrange index (from A to Z ) or related contentsthis is the index look like
 this is the contents look like
this is the contents look like if you want search for any specific thing just click search
if you want search for any specific thing just click search click Using Help to get the most form cisco help system
click Using Help to get the most form cisco help system
This is cisco glossary cisco explain every acronym they use in this glossary
 need more help at bottom for each ( interface or Page ) you found How do I ?
need more help at bottom for each ( interface or Page ) you found How do I ?just click select the related question you need and click go

now you are familiar with CISCO SDM and interfaces (pages)
CISCO SDM is a best piratical way if you want learn how to do things in CLI